Topics at the Allianz Center for Technology:
The virtual vehicle key

August 2018
Theft is a relevant topic for auto insurance and leads to high average claims amounts. This results significantly increased claims costs for a large number of vehicle models.
For this reason AZT has, amongst other things, been working on vehicle theft prevention for several decades. A significant result in this regard was the introduction of a legal requirement for electronic immobilizers in newly registered vehicles from 1998, which was based on the standards and requirements developed by experts at AZT.
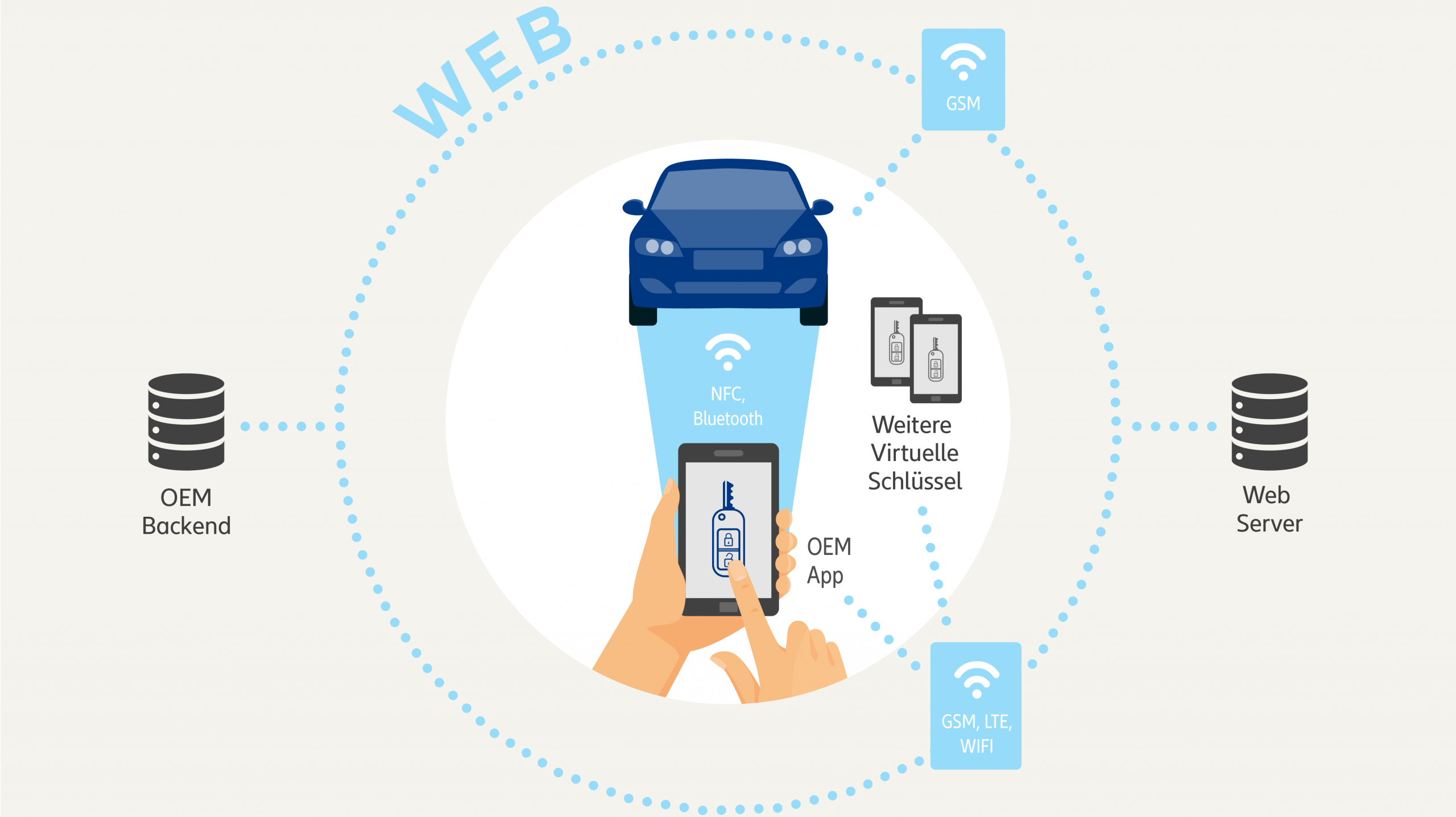
Currently the development and integration of electronic components in the automotive industry is entering a new dimension as more and more innovative and networked comfort and customer functions are launched on the market. Among other developments, the first OEMs are now also starting to offer their customers a virtual key as an additional option alongside the conventional physical car key when purchasing a vehicle. So the smartphone is becoming a car key. In future, the driver will use the app to unlock and start the vehicle; the key is going virtual.
Virtual keys and other digital after-sale services rely on globally networked systems. The keys bring with them not only an increase in comfort but also new attack vectors on the interfaces between the entities in these networked systems. What about data security for example, what happens when the system is hacked?
The technology also leads to many questions for insurance, in particular in the case of total theft. Until now, the customer would present the complete set of keys to the insurer for the settlement of the claim. In principle, this also applies for the virtual car key. No customer will want to send their smartphone to their insurer in the case of total theft.
To counter these challenges, AZT analyzed the virtual vehicle key system, and looked at the current and potential future risks and attack vectors in order to formulate the requirements for virtual vehicle keys. This resulted in guidelines covering the design of virtual vehicle keys as well as the storage and processing of the respective data. With this, auto manufacturers are given a set of guidelines, applicable to all technologies and manufacturers, that serve to retain or increase the level of protection offered to the customer and their vehicle by the current immobilizers.
The four most important requirements for the virtual vehicle key
The virtual vehicle key must not be able to be copied, and, as with a physical key, the number of keys in circulation must be transparent.
A clear, transparent and fixed list of all authorized vehicle users must be available to the customer, and to the insurer in a loss event. In the case of total theft, the customer must also be able to immediately revoke all virtual keys in a demonstrable manner.
Authorization to enter the vehicle must be separate from authorization to drive the vehicle, so as to not undermine the existing layer of protection offered by the electronic immobilizer and to ensure the security of future service models such as "Delivery to the car boot".
The data environment used to access and store the virtual key must be completely separate from other applications. The processing and storage of all security-critical data, such as authorizations and key calculations, must be confined to a secure storage and execution environment.
A full description of AZT's requirements for virtual vehicle keys can be found here:
Requirements for virtual vehicle keys
Pictures and videos

Authorization to start engine by means of virtual vehicle key

Attack vectors on the ecosystem virtual vehicle key
Ecosystem virtual vehicle key